Twitter recently released a transparency report about its users’ adoption of two-factor authentication, and the report wasn’t exactly encouraging. Only 2.3 percent of Twitter account had at least one 2FA method enabled, and of those, 79.6 percent had SMS enabled, 30.9 percent had a TOTP application enabled, and 0.5 percent had a security key enabled.
Twitter can’t do much about its users’ apparent lack of interest in enabling 2FA, but it only has itself to blame for the fact that so many 2FA users rely on SMS.
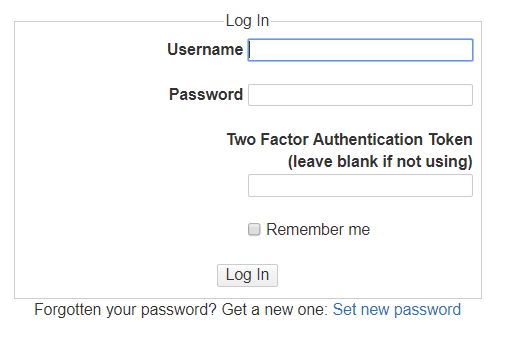
The last time I created a new Twitter account for a specific project I was working on, one of the first things I wanted to do was enable 2FA.
However, it was impossible to enable 2FA without first enabling SMS 2FA. I have no interest in using SMS as a 2FA method, but Twitter insisted I do so anyway.
I suspect that Twitter did this so it could collect my phone number. I cannot imagine any other reason it would not simply let me set up a TOTP app for 2FA out of the gate.
Instead, I had to enable SMS 2FA and confirm that. Then, I was able to add my TOTP application to the account. Finally, I went in and removed the SMS 2FA from the account.
That was a ridiculous number of hoops to jump through and all too common of a 2FA onboarding process across many systems.
Fortunately, Twitter seems to have abandoned that practice, but it is ridiculous that anyone ever thought that an acceptable practice in the first place.