On May 12, the WannaCry ransomware began spreading across Europe, with its most high profile victim begin the UK’s National Health System. It was widely reported that the NHS was hit hard, in part, because it was still relying on Windows XP for a large part of its infrastructure.
On May 14, someone Tweeted this article into my timeline disputing that. According to Matthew Schwartz writing at HealthCareInfoSecurity.com,
Based on new information, however, part of the problem appears to be that many NHS trusts didn’t pay for extended Windows 7 support.
“I think what is also becoming clear is that the NHS impact was a result of lack of patching Windows 7 rather than outdated XP,” Alan Woodward, a professor computer security at the University of Surrey, and a cybersecurity adviser to the EU’s law enforcement intelligence agency, Europol, tells Information Security Media Group.
“If this is the case then it shows that there is a lack of resources across the NHS IT estate,” he adds.
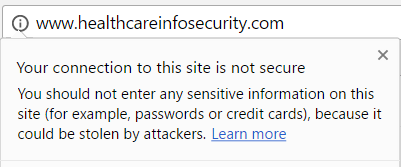
Interesting news, but I want to point something about the website posting this information. Although it is dedicated to covering infosec in health care, the site itself can’t be bothered to use SSL on its website.
Which is bad enough because it would open users of the website to trivial MITM attacks. But it gets worse. You an apparently pay these yahoos for a premium version of their offerings. And, of course, the login page for account access doesn’t use SSL either.

Part of the issue with infosec in large organizations is these sort of pretenders who can’t be bothered to implement the most basic of security measures and yet will try to convince the CIO or CEO that they need to direct part of your company’s infosec budget their way.